Tamper Evident RFID Tags
Introduction
Choosing the right RFID tag for your application can be one of the more difficult parts involved with implementing a system because there are several factors like size, read range, attachment method, encasement, cost, etc. involved.
Deciding which tag is the best fit can be even more complicated if the tag needs to meet additional requirements, such as withstanding extreme temperatures, ATEX certification, or to be tamper evident. RFID tags can be used as additional security if a product or item needs to show or hold up to tampering.
Tampering Terminology
Tampering – Tampering occurs when someone or something interferes with an item or product to cause damage or make unauthorized alterations. It is most commonly used in reference to products, but also can be used to describe machinery or equipment.
Tamper Evident – Tamper Evident describes a process or device that makes tampering easily noticeable. For example, the process outlined and regulated by the Food and Drug Administration (FDA) involves one or more barriers of entry, and usually has text indicating not to use the product if any seals or barriers are broken.
Tamper Resistant – Tamper Resistant describes a process or device that is designed to resist access to the product. For example, Tamper Resistant packaging can be shrink-wrap on fresh food, or beverages that have been sealed. Tamper Resistant packaging varies in levels, depending on the company and type of product, but can also be standardized.
Tamper Proof – Tamper Proof describes various methods of preventing and detecting tampering that relate to item security. Tamper Proof can indicate the use of a locking mechanism or device in a high security product like high-value electronic items or can be a highly secure seal that cannot be replaced once removed.
Who Uses Tamper Evident Packaging?
Besides the pharmaceutical industry, specifically over-the-counter medicine, tamper evident packaging is used in shipping high value equipment or sensitive documents, food and beverage containers, and vehicle car tags that contain account or personal information (e.g. tolling passes and parking lot access labels).
Tamper evident labels, seals, or plastics are also used in the logistics portion of the manufacturing supply chain to ensure that items are not tampered with or stolen during transport.
How is RFID Incorporated into Tamper Evident Packaging?
Tamper evident packaging isn’t required to be uniquely identified with an RFID tag or barcode, but adding an RFID tag could increase the functionality of packaging and enable visibility into which item has been opened.
RFID tags can be incorporated both into the packaging, and in addition to the packaging, depending on if the item needs to have added security to make it tamper proof (vs. just tamper evident).
Examples of what Tamper Evident Packaging + RFID can Provide:
1. Tamper Evident + Authentication
Combining tamper evident packaging with product authentication methods can be accomplished using RFID tags. Currently deployed for high-end food and beverage products, like wine and spirits, RFID tags both provide item authentication and that the item has not been tampered with. Using a similar tag as the one below, the long portion of the tag is adhered down the neck of a wine bottle during packaging.
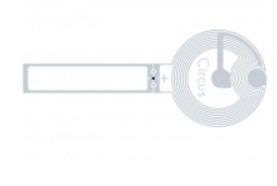
If the tag is UHF, restaurants can be outfitted with handheld RFID readers, and staff can locate and read a bottle’s RFID tag and ensure that it is authentic. If the tag has both an NFC and UHF tag, or just an NFC tag, consumers can scan the bottle via an NFC-enabled smartphone to confirm the bottle is authentic before purchasing.
2. Tamper Evident + Item/Account Information
In instances of tolling accounts, access control to secure parking lots, or vehicle identification, users are provided with labels or tags to place in their vehicle. These tags contain account or vehicle information; if stolen, lost, or abused, there could potentially be serious consequences depending on the application and information available on the tags. Because RFID tags typically contain a random number that is associated in a database with a user’s information, even if a tag is stolen, pertinent information would be very difficult to obtain.

So, what part of these labels need to be tamper evident? To ensure that these RFID labels are not used fraudulently on vehicles that they are not assigned to, companies create a tamper evident or tamper proof backing that adheres to the vehicle’s windshield. Upon removal, the tag can destruct via tearing, or send a different signal once tampered with upon interrogation. Similar tags are available formatted as padlocks or wire tags for securing containers.
3. Tamper Evident + Traceability
High cost machinery or electronics are shipped across the world on pallets or in returnable containers. Manufacturers want to ensure that they are not stolen or tampered with during the shipping process because these items are so valuable. By locking the containers with padlock, wire, or zip tie RFID tags, the manufacturer can guarantee (up to a certain point) that they are safe and will reach their destination. Throughout the shipping process, the tags can be scanned and read continuously in order to update their location.

The tags are then scanned upon arrival and the data is automatically sent back to the manufacturer. Once the valuable products arrive, the tags are broken, and the containers opened to unload the equipment, then the containers can be sent back to the manufacturer for another shipment
4. Tamper Evident + Tamper Alarm
In cases where extremely high-value items need to be constantly monitored in a warehouse, or during shipping, RFID tags can be attached to the item, providing an additional level of security. Certain RFID tags have functionality that, once the tag is broken, it cannot be read via RFID readers in the area. Once the RFID reader no longer reads those specific tags, a visual and audible alarm can be automatically triggered and alerts can be sent to the appropriate personnel.
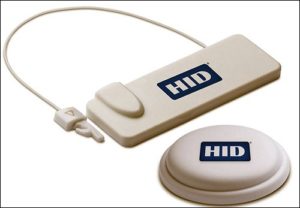
Some RFID tags (e.g. HID Global’s SealedTamper UHF Tag below) are programmed to still respond to interrogation when the item has been tampered with, only the response is modified and differs from the non-tampered with response. This way, users can locate the tagged item that has been tampered with, instead of responding blindly to the item’s last known location.
Conclusion
To learn more about tamper evident RFID tags and their role in an item’s security, comment below or contact us!
If you would like to learn more about all things RFID, check out our website or our YouTube channel.
To read more about RFID tags, check out the links below!